By now, most of us know that Microsoft Teams is built on Office 365 Groups. Additionally, many customers had been using Office 365 Groups for some of their collaboration before Microsoft Teams was released. That means that there are a number of Office 365 Groups out there, that may need to be converted to Microsoft Teams. The general process for using an Office 365 Group as the foundation for a Microsoft Team is well documented, and it would seem to be fairly straightforward. However, as anyone who has actually done this knows, it isn’t quite that simple.
The purpose of this article is to help you move the data that may exist in your Office 365 Group – such as email, OneNote, Planner, etc…over to a newly created Microsoft Team.
We’ll start with a brand-new Office 365 Group, create some content and then convert everything over to a new Team.
Let’s get started…
Creating the Office 365 Group and Populating it with “Stuff”
Let’s start by creating a new Office 365 Group so we know exactly what happens.
Here, I am creating an Office 365 Group named O365-TeamsUpgrade. Notice that it has been created with the default Privacy setting of “Private”.

Next, I add some of my team members to the Group.

Now my Office 365 Group is ready to go, and I have all the usual things in my configuration.

I can send email to the group, because every Office 365 Group has an associated email address. As expected, the email and meeting invites show up in the Office 365 Group mailbox, which exists in Exchange Online.

I go to Files and create a Word document.

Next, I go into my Notebook and create some content in the Office 365 Groups OneNote

I can go into Planner next and create some content there….


Lastly, I click on the Site link and I see the SharePoint Site.

If I go to the Documents library I see the Word document that I created just a few minutes ago.
So, we all agree I have legitimate content in my Office 365 Group, right? Right.
Okay, now comes the fun part –converting it to Microsoft Teams.
Upgrading to a Microsoft Team
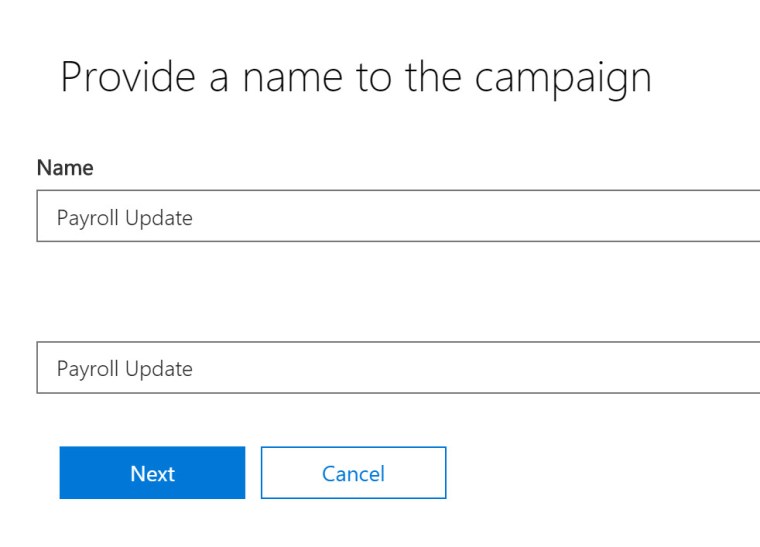
In my Microsoft Teams client, I click “Add team”.

Next, I click on Create team.

In the next dialog box, I can create a brand-new Team, or as shown below, I can create one from an existing Office 365 Group. That’s what I want to do, so I click on that link.

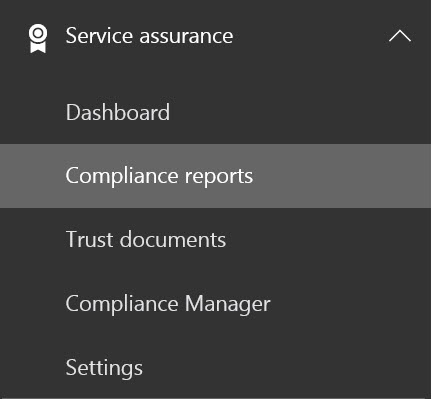
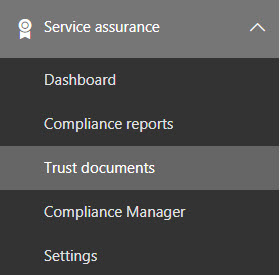
It now provides me with a list of the Office 365 Groups for which I am the Owner, and which are set to Private visibility.

I click the radio button and click Create team.
NOTE:
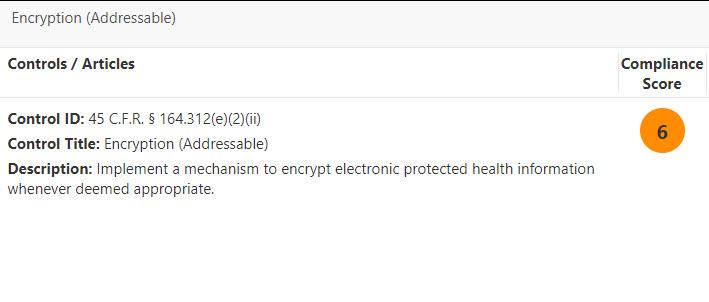
When upgrading an Office 365 Group to a Microsoft Team, there are several points that you must keep in mind:
You must be the Owner of the Office 365 Group
The Office 365 Group visibility must be set to Private. If it is not set to Private, you can set it to Private long enough to do the switch and then turn it back to Public once you’ve switched it over to a Microsoft Team.
There cannot be a Team that already exists with the name of the Office 365 Group you intend to convert. If it exists already, you’ll end up with two disconnected objects. For example, I created a brand-new Team with the same name as my Office 365 Group.

It lets me create the Team with that name, but it doesn’t bring over any of the content from the Office 365 Group with the same name.

Lastly, Teams doesn’t support these characters: ~#%&*{}+/:<>?|'”.. This, if any of your Office 365 Groups are named using those characters, you won’t be able to convert them to a Microsoft Team without renaming them.
Not cool, man…not cool
So far, everything is going just swimmingly, wouldn’t you say? Now I just open up my brand-spanking-new Microsoft Team and I see all the stuff from my old Office 365 Group, which has been converted over, just like magi……..wait….what happened? It only moved over the group membership? Where’s my super important Word document???? Where’s my Planner? Where’s the OneNote?

Let’s investigate…
Files
If we go back to our Office 365 Group (it still exists), we see our Word document still sitting in the Files area. On the far-right side, click on “Browse Library”.

Microsoft Teams stores documents and files in a folder in the SharePoint Document Library which is named for the Channel. By default, the only channel that exists in a new Microsoft Team is named “General”. Therefore, the SharePoint library shows me that my Word document is sitting outside of the General channel, as you see below.

If I select my Word document and click on the ellipsis, I can choose to move the document.

Let’s move it to the General folder. You can move all of your documents to the General folder, or if you have more channels in your Team, you can move them to any channel you like.

I now go to my Team and there’s my Word document in the General folder!

OneNote
But wait, I also had some business-critical information in OneNote. Where did that go?
Well, unfortunately there aren’t any really great options for moving your OneNote from an Office 365 Group over to a OneNote in Teams.
Here’s one way to do it:
In your Teams client, go to the channel of your preference, and click on the “+” sign to add a tab to that channel. In this case, I’m adding a tab to the General channel.

You’ll be presented with a number of options. Select the one that says OneNote.

Create a new OneNote notebook, and name it whatever you like. For my example, I’ll name it O365-TeamsUpgrade01

If I go back now to my Office 365 Group, I see the newly created OneNote notebook, and it exists beneath the notebook that existed already.

Now I can copy the individual pages from one notebook to the other. I right-click on the page and select “Copy”.

I switch over to the new notebook, right-click and select “Paste”.

For my example, I deleted the “Untitled Page” and I’m left with only the page from my original OneNote.

And back in my Microsoft Teams client, everything looks good as well.

Planner
Mercifully, moving your Planner files over is relatively easy.
First you go into the new Microsoft Team and select the “+” sign to add another tab to the appropriate channel. Click on the Planner icon.

In the next dialog window, select “Use an existing plan”, and from the drop-down menu, select the name of the appropriate Office 365 Group.

And just like that, all your Planner information is switched over to Microsoft Teams.

Email
The last thing that needs to be converted over is email.
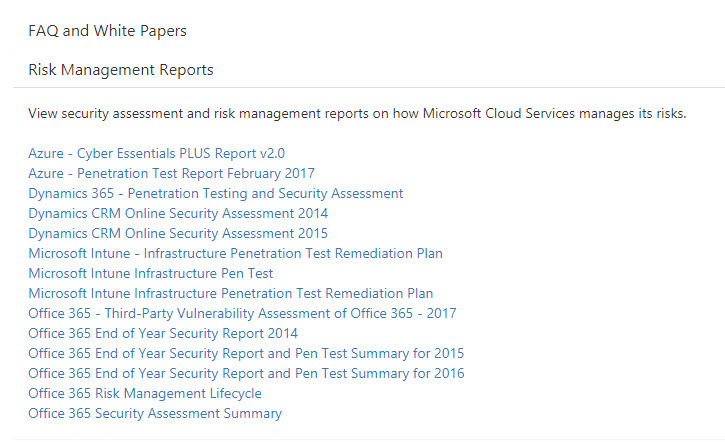
Again, there unfortunately isn’t a great story there yet. Here’s one idea that you can use.
As we have seen, each Team channel has its own email address. You can get that email address by going to the channel (such as General), clicking the ellipsis and selecting “Get email address”.

Copy the SMTP address, which is the section that’s highlighted below – 62057b2c.microsoft.com@amer.teams.ms (Yours will be different).

Now, go back to your Office 365 Group, select the email you want to move and click on “Forward”. In the new email window, copy the email address for the Teams channel into the “To” field in the email and click “Send”.

Go back to your Teams – General channel and you’ll see the email that has been forwarded from the Office 365 Group email inbox.

This is definitely not the easiest process in the world, and it tends to be error-prone if you have lots of email, but it will get the email conversations moved over.
Now, there may still be some people who will accidentally use the Office 365 Group email address. How do you account for that? One way is to add the new Microsoft Team as a member of the Office 365 Group.
Go in to the membership of the Office365 Group and click “Add members”.

In the dialog window, select the email address of the Microsoft Teams channel where you want the new emails to be delivered.

In my case, I select the email address beginning with “62057b2….” and click “Save”.
Next, go into the Group settings and select “Manage group email”.

In the dialog box, select “Follow in inbox” and click “Save”.

Now, when an email is sent to the address of the Office 365 Group, it is also sent to the email address of the Microsoft Teams channel that I have designated, as you can see below.

Well, that was easy, wasn’t it?
Obviously, I’m being a little sarcastic…this isn’t the easiest process, and there are certainly ways that much of it can be scripted, but for a quick and dirty way to move a few Office 365 Groups over to Microsoft Teams, it should be sufficient for your needs.